Okta
Okta Walkthrough
This page provides a guide for configuring Okta to utilize authID's biometric authentication platform.
This page assume users are using the Okta Identity Engine and you have features such as Custom IdP Factor authentication enabled.
Authentication Scenarios
Below are a few common scenarios users can try to solve with the authID platform. Each section includes links to other parts of the page to help create a solution that best suits user needs.
Protect All Critical Areas of Okta
-
Recommended Approach: Passwordless Login and Biometric/Passkey Multi-factor Authentication
-
Used When: The user required the strongest protection across all areas of the user's Okta instance
-
Benefits,
- All areas of Okta are protected.
- True passwordless login and seamless biometric MFA.
- The strongest combination of authentication factors.
How to Implement,
- Add authID as a Factor-only IdP
- Add another authID IdP in SSO Only mode
- Create a routing rule to activate the SSO IdP at login
- Add IdP Authenticator and set Enrollment policy
- Create Authentication Policy to apply Factor-only IdP in certain situations.
Protect User Logins
-
Recommended approach: Passwordless Login with Biometric/Passkey.
-
Used when: you want to increase login security and potentially eliminate passwords.
-
Benefits:
- Replace or augment traditional MFA with stronger biometric authentication.
- Potential to eliminate passwords.
- the less friction at the login.
-
How to implement:
Protect instance features and account/device recovery
-
Recommended Approach: Biometric/Passkey Multi-factor Authentication.
-
Used When: The user required, certain functions to be protected with biometric controls, or the user required to increase security around account and device management.
-
Benefits,
- Granular application of authentication factors.
- Secure account/device recovery and management.
-
How to implement,
- Add authID as a Factor-only IdP
- Add IdP Authenticator and set Enrollment policy
- Create Authentication Policy to apply Factor-only IdP in certain situations.
Video Walkthroughs
Add New Identity Provider
The following video demonstrates adding the authID integration the user created earlier to Okta.
[](https://player.vimeo.com/video/790223827?h=3b7bc50022
Configure Policies
The following video demonstrates the use of new Identity Providers in common authentication scenarios.
[](https://player.vimeo.com/video/790223675?h=161f64774f
Setup Steps
These steps are not ordered and can be used as required by the user solution.
Add Identity Provider in SSO Only mode
- Begin by adding an identity provider to your system.
- Then, configure a routing rule to enhance user login security by integrating the newly added identity provider.
- Navigate to the Security > Identity Providers section of the user dashboard and click the labeled Add Identity Provider.
- Select the tile marked OpenID Connect.
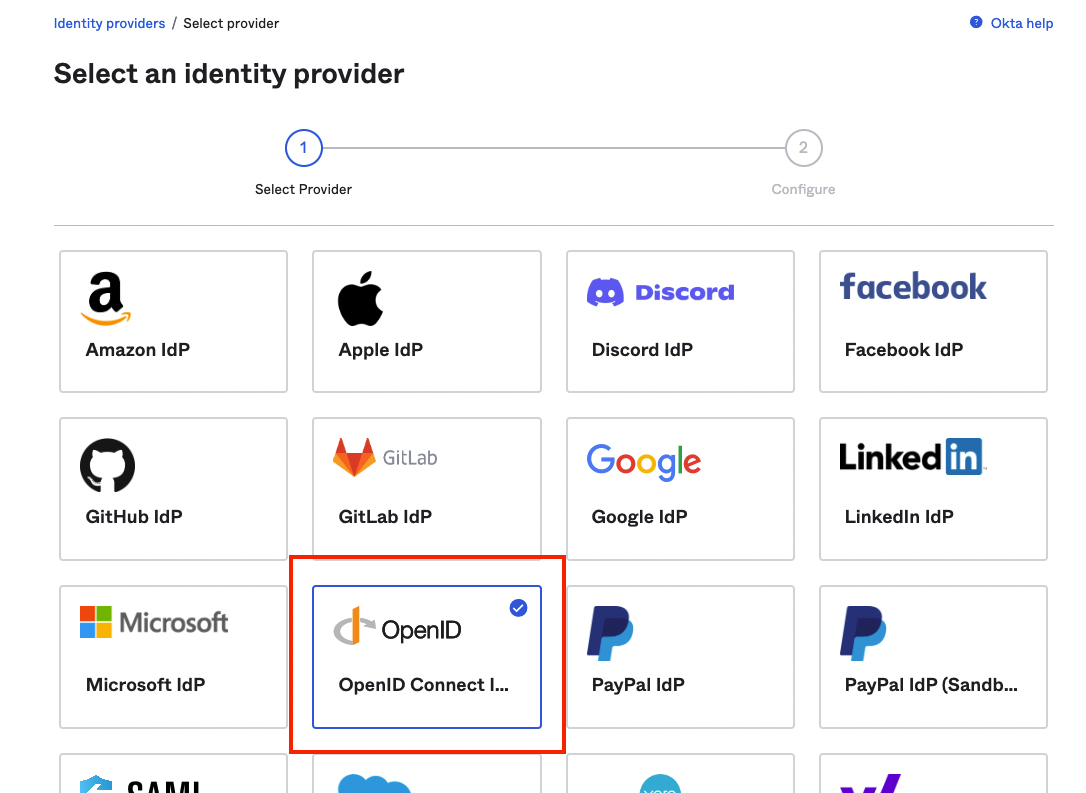
Choose OpenID Connect.
- Specify a Name for the connection. Ensure that the IdP Usage field is set to SSO only. Next, use the saved values from your AuthID integration to fill out the Client ID and the Client Secret fields.
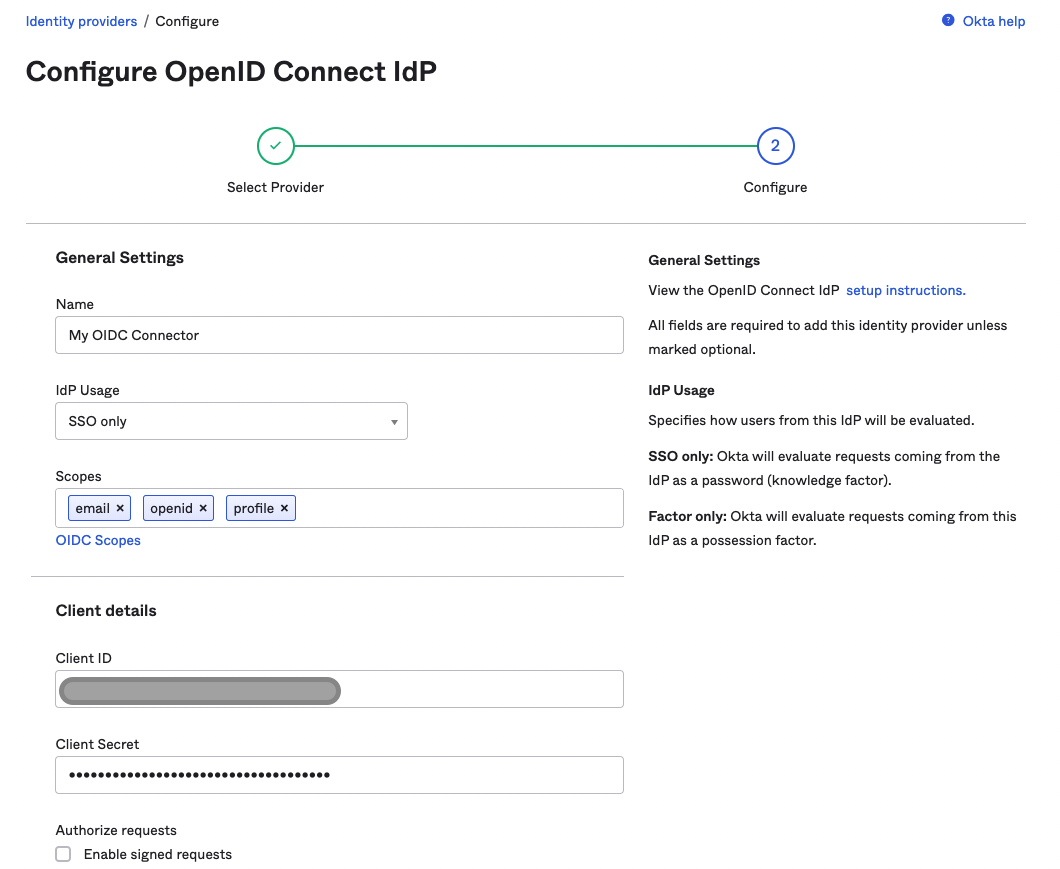
Configure OpenID Connect.
- Fill out the Endpoints section with the following values from the AuthID OIDC server:
- Issuer:
https://id.authid.ai/oidc/webAuthorization Endpoint:
https://id.authid.ai/oidc/web/connect/authorizeToken Endpoint:
https://id.authid.ai/oidc/web/connect/tokenJWKS Endpoint:
https://id.authid.ai/oidc/web/.well-known/jwksUserinfo Endpoint:
https://id.authid.ai/oidc/web/connect/userinfo- Finally, specify user-preferred Authentication Settings and then JIT settings if applicable. Save to create the Identity Provider.
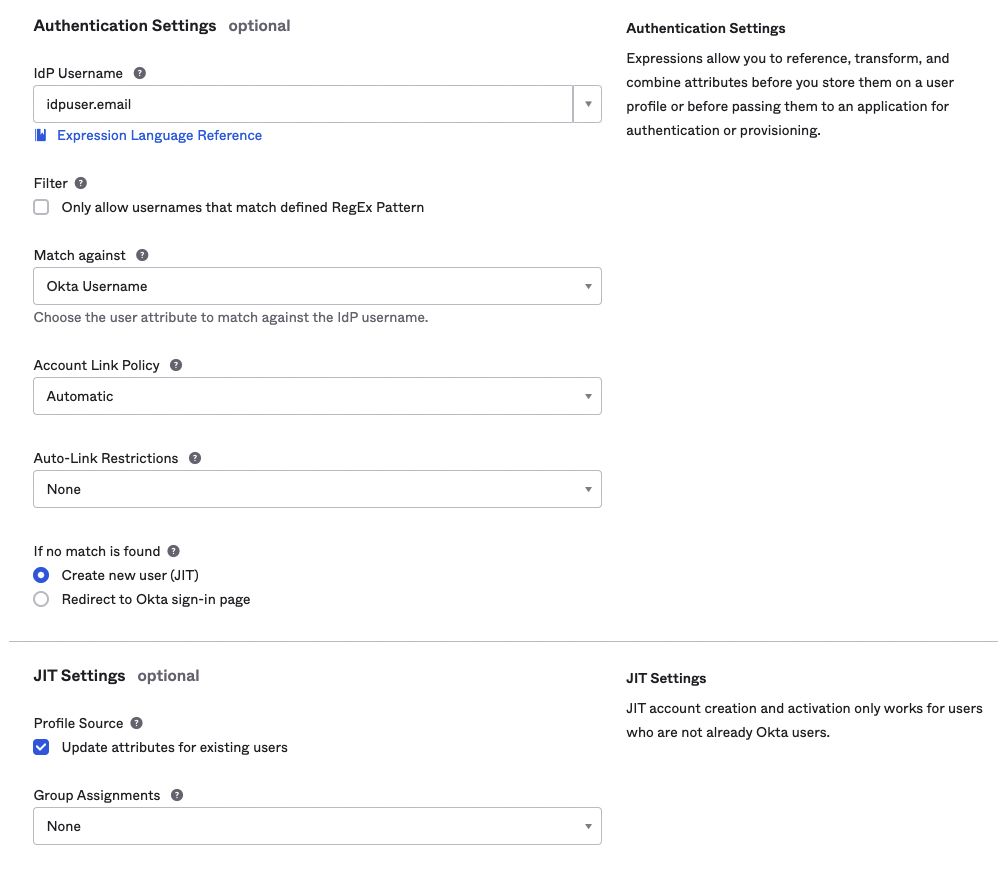
Authentication Settings.
CAUTION
Once the identity provider has been created, you must ensure that at least one value from the Login redirect Urls parameter for your authID integration matches the Redirect URI. This value can be found by clicking on the identity provider in the list: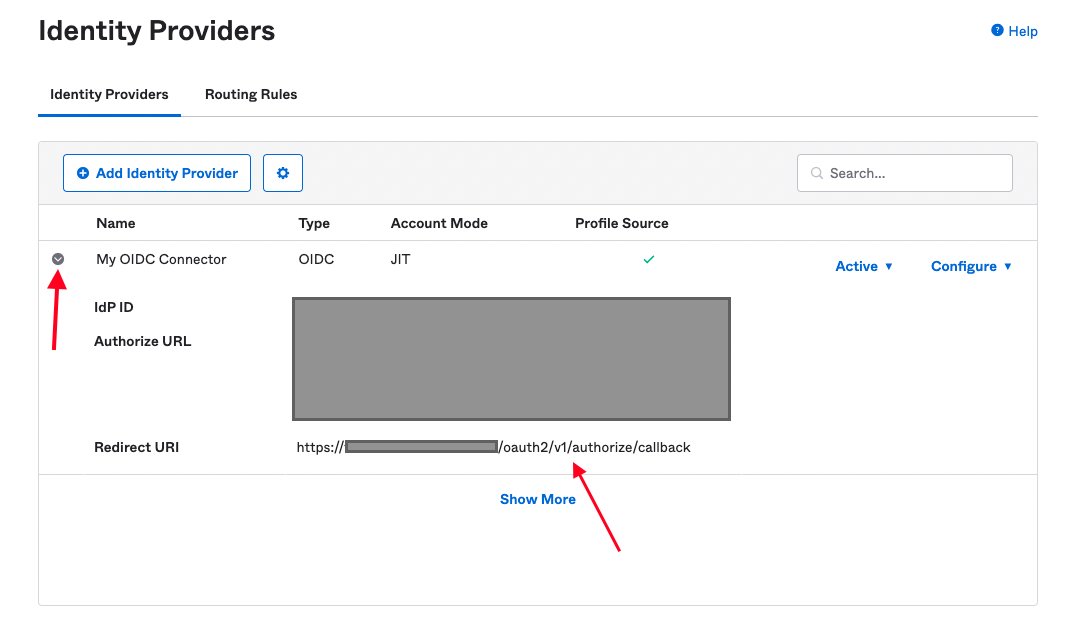
Add Identity Provider in Factor Only mode
Follow the sections to create an integration in authID, and then use the same directions to create an identity provider in SSO-only mode but be sure to edit the settings of the new IdP so that it is set to Factor only for the IdP Usage, as seen in the screenshot below:
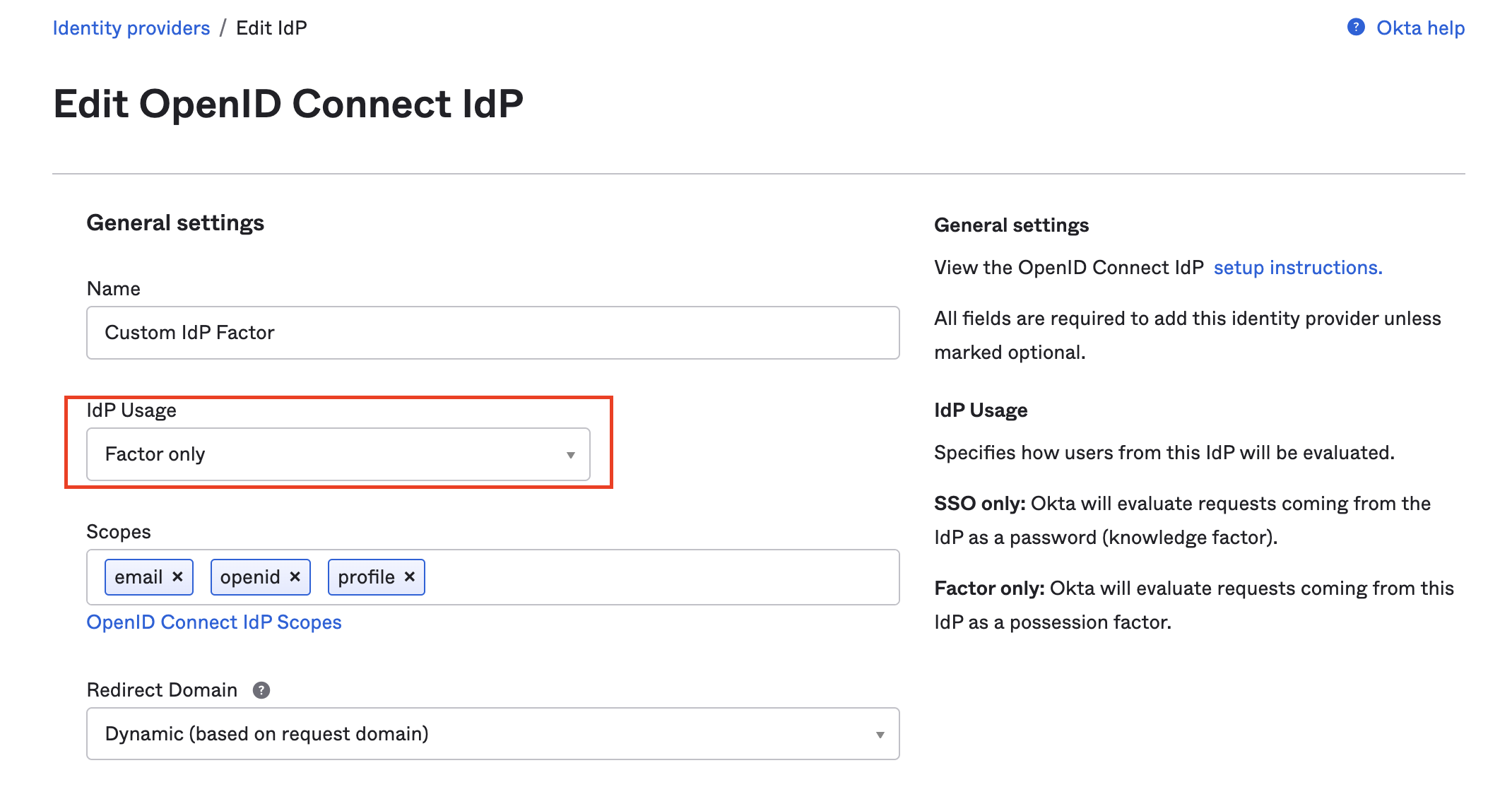
General Settings.
Add Routing Rule
Routing rules play a crucial role in guiding users to the most suitable identity provider based on their compliance with pre-defined conditions. By applying these rules, we can effectively determine whether a subset of users should be directed to the OIDC identity provider that we have set up.
To begin,
- Navigate to the Security > Identity Providers section of the user dashboard.
- Select Routing Rules tab.
- Click Add Routing Rule to open the modal for creating a rule.
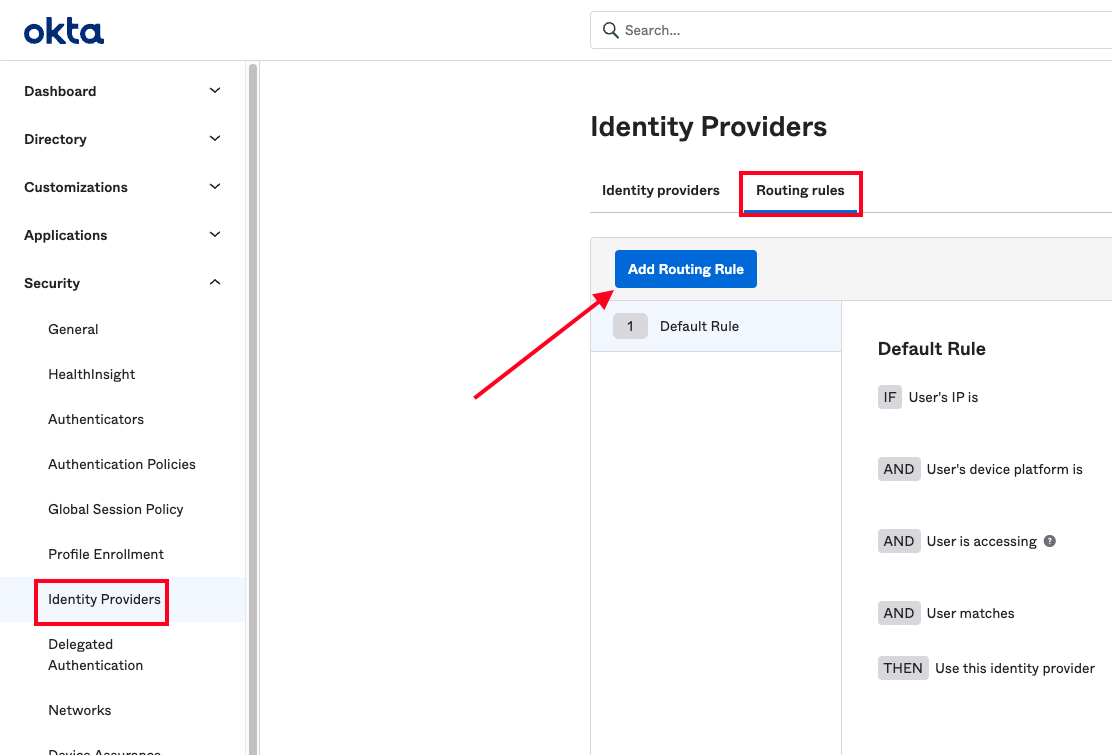
Add Routing Rule.
The user can configure the rule, and ensure the last section labeled Use this identity provider points to the identity provider created earlier. For example, this rule routes any users attempting to access the app integration user created previously with an @example.com email address to use the OIDC connection.
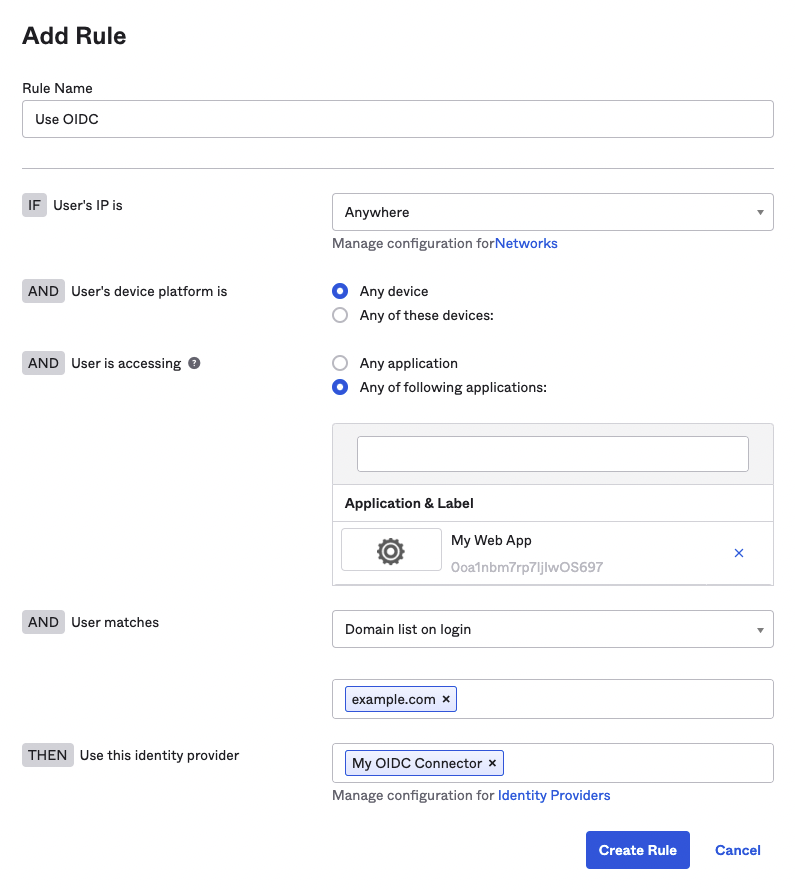
Add Rule.
Add Custom IdP Authenticator
- Next, add the Custom IdP Authenticator by navigating to Security > Authenticators and click to Add Authenticator.
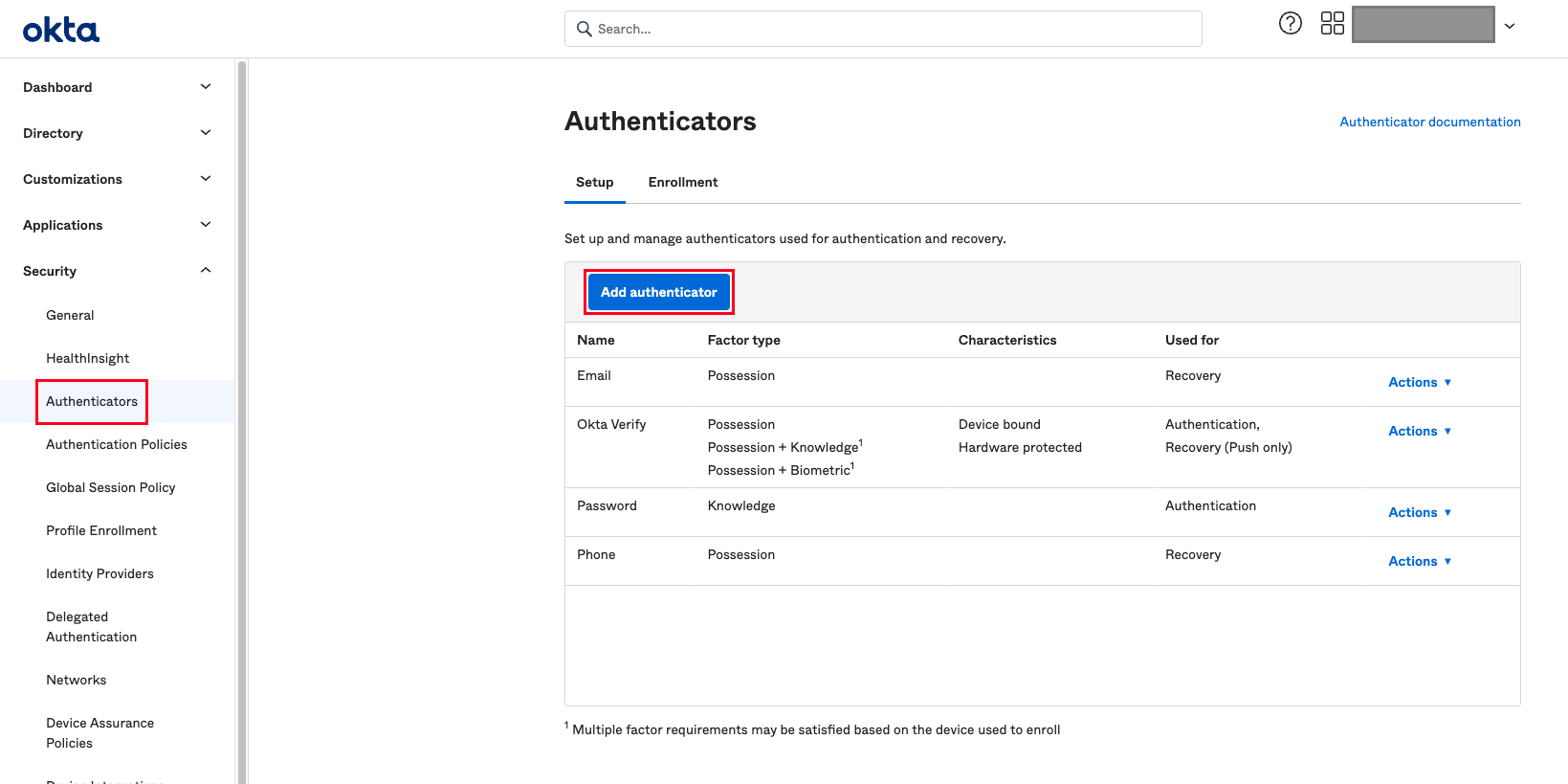
Add Authenticator.
- Select IDP Authenticator from the dialog.
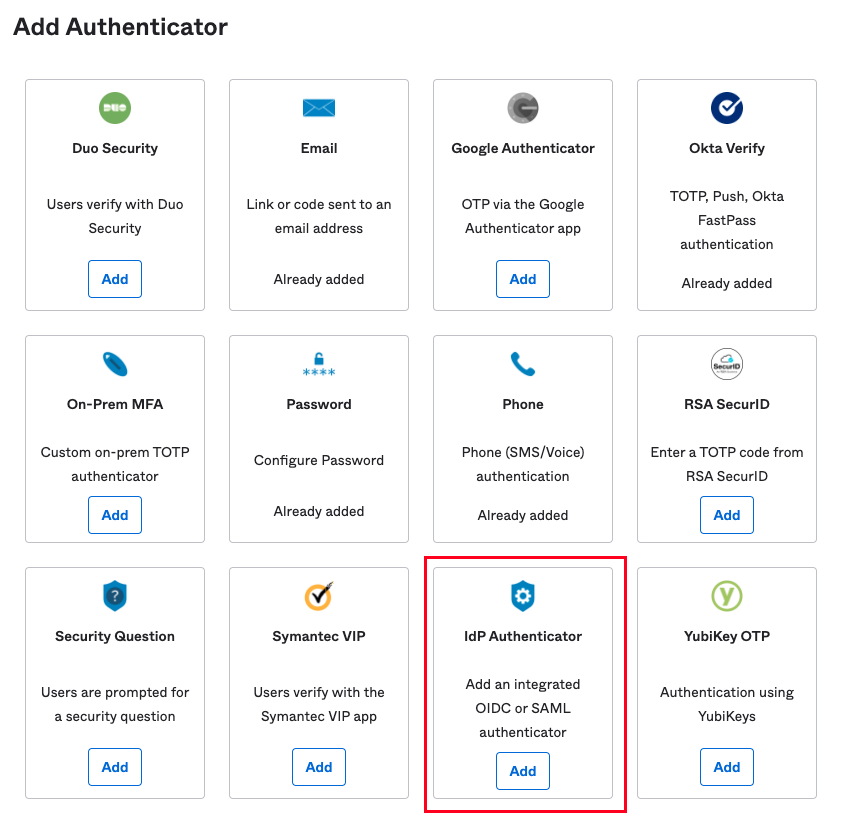
IDP Authenticator.
- Choose the IDP you created earlier from the dropdown and click Add.
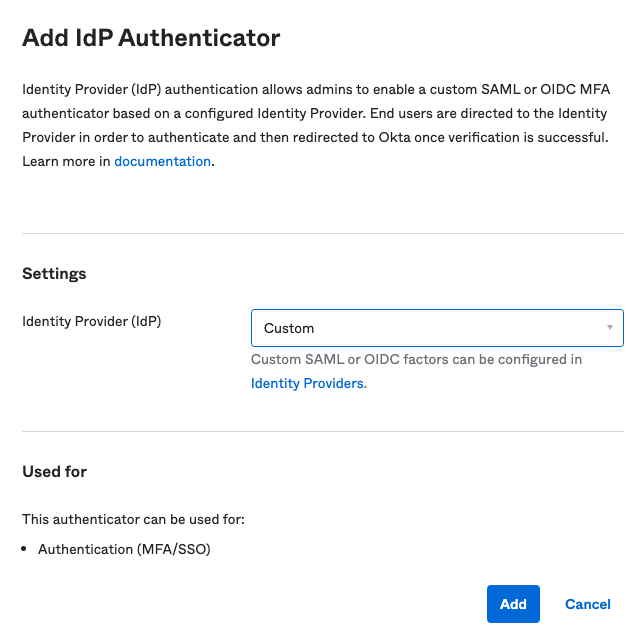
Add IDP Authenticator.
- User choose the authenticator from the list of available authenticators.
Testing Custom Authenticator
- When a user clicks on the resource or feature protected by the authID custom IdP Authenticator, it prompts to enroll the authenticator to their account:
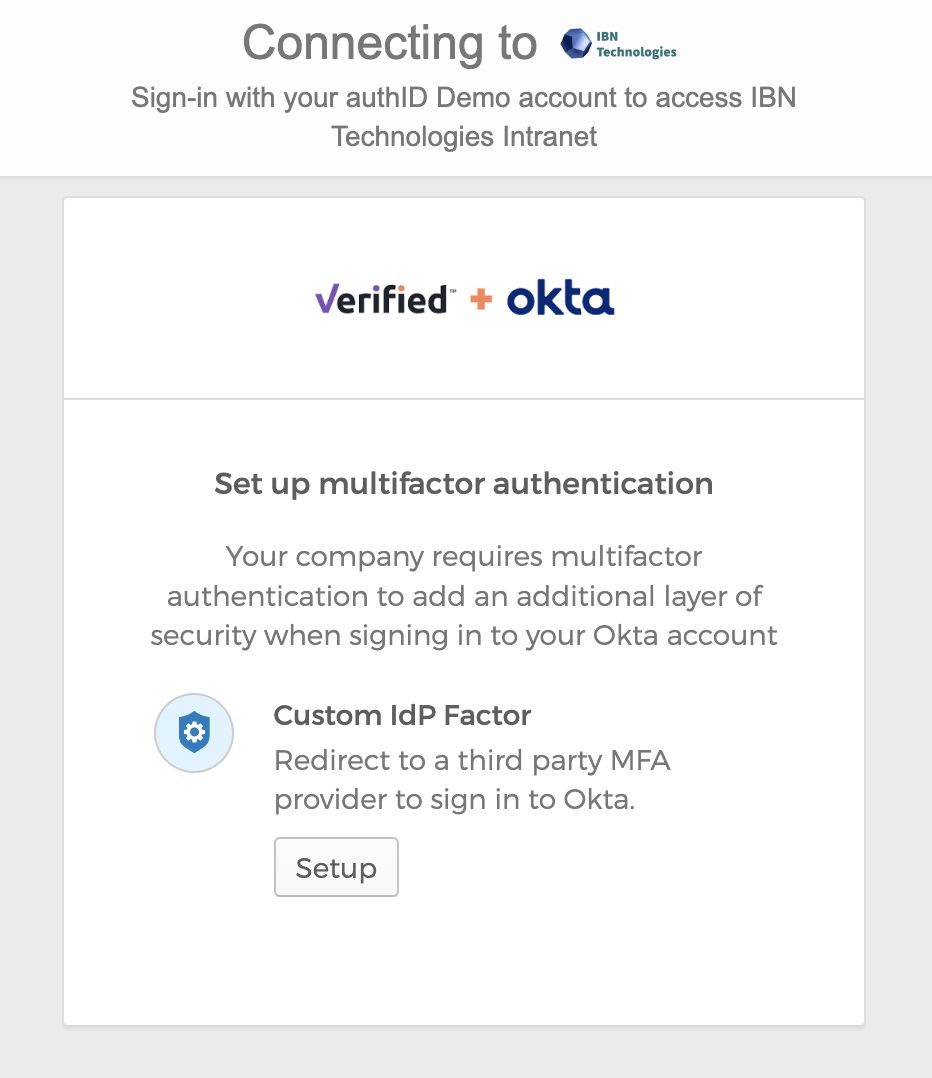
Custom Authenticator.
- Depending on user integration configuration, and the user is prompted to enroll their selfie, passkey, or both. Below the user is being asked to enroll only their selfie:
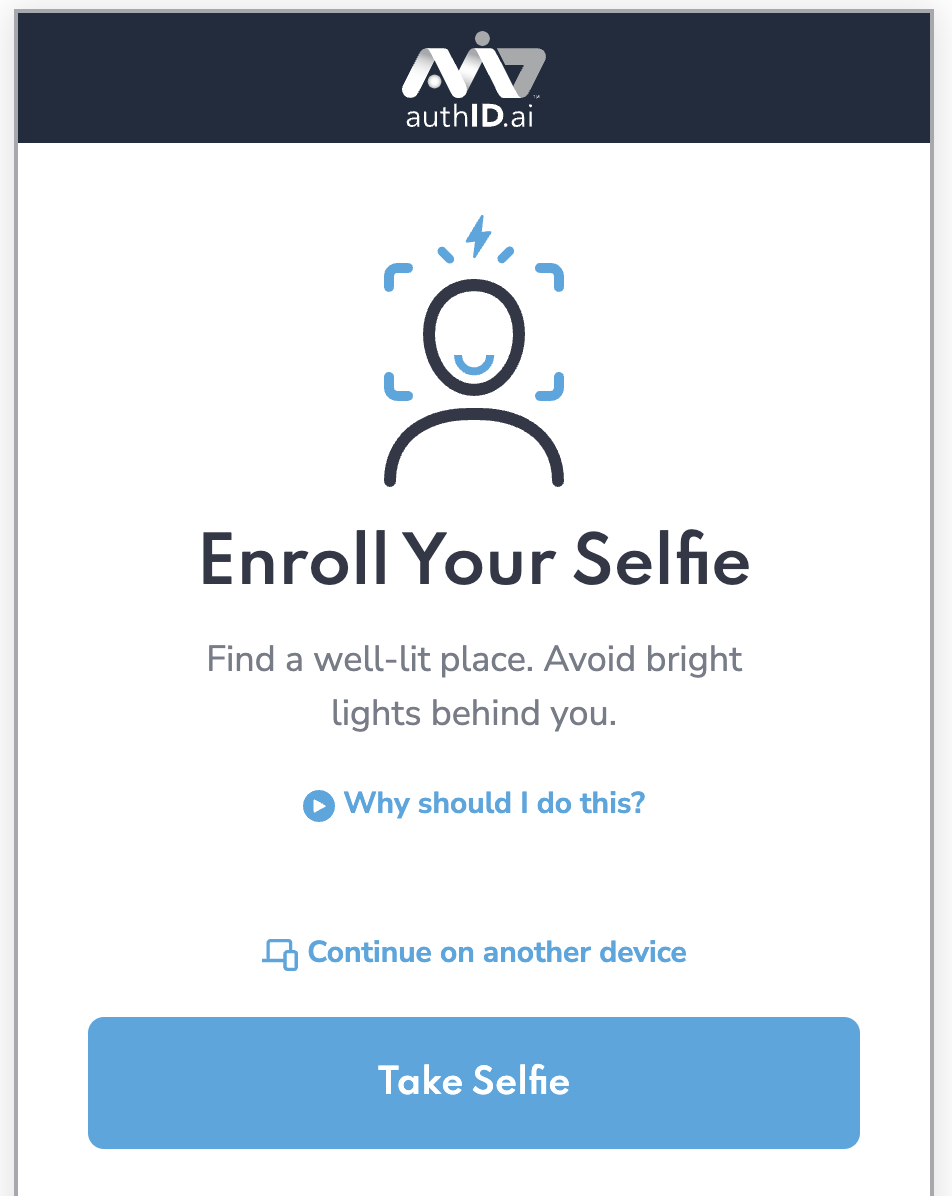
Enroll Your Selfie.
- Once this is complete, the authentication must proceed and a user is allowed to continue the action that triggered the MFA challenge. When the user attempts the same action on subsequent occasions, it is prompted by Okta to verify their identity using this authenticator:
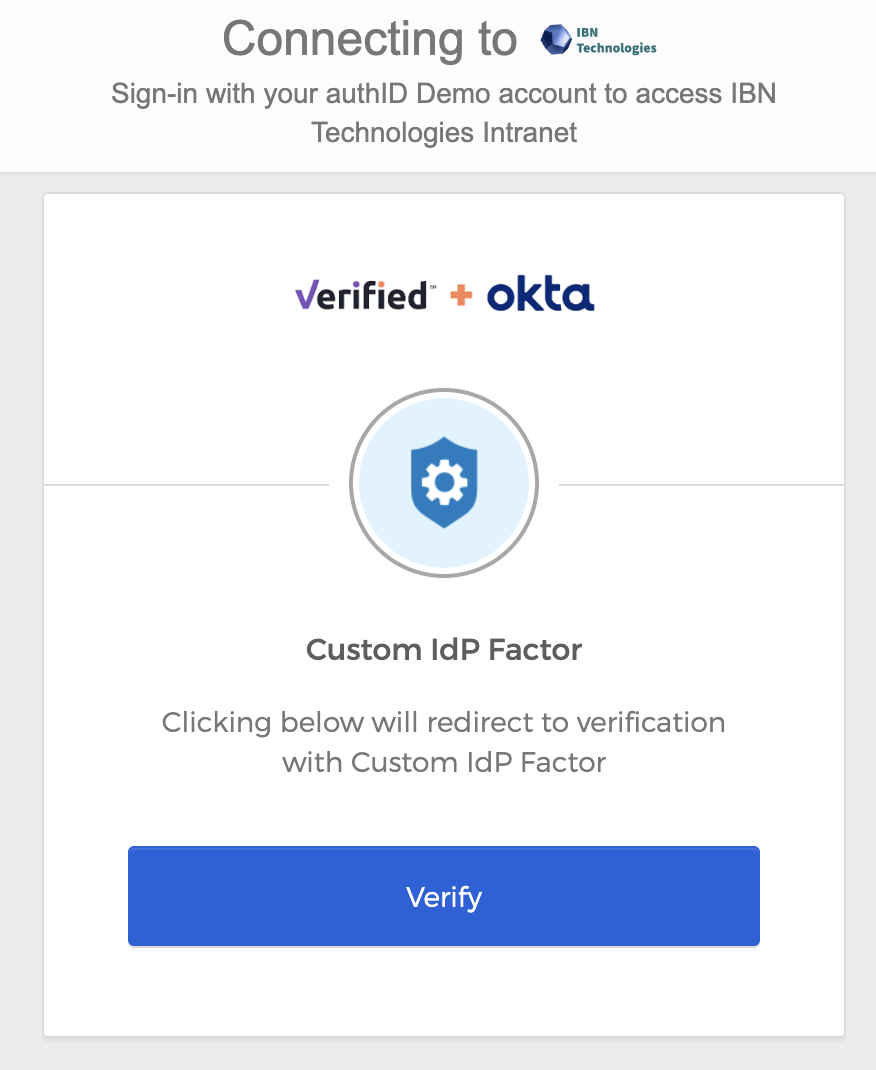
Custom IDP Factor.
Set Authenticator Enrollment Policy
It is recommended to present enrollment options to the users for the new authenticator type, and users can craft policies on how and when this happens.
- Navigate to Security > Authenticators and click the Enrollment tab.
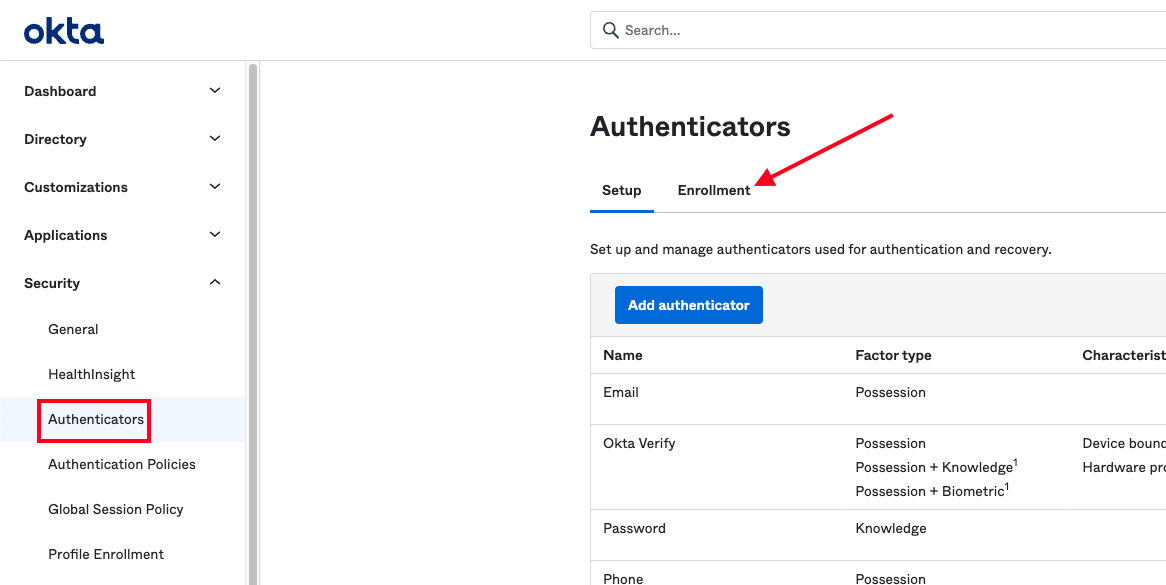
Enrollment.
- User can either add a new policy or edit an existing one. In this example, the user edits the Default Policy and enables the IdP Authenticator as an eligible authenticator.
- Select the policy from the left-side list and click the Edit.
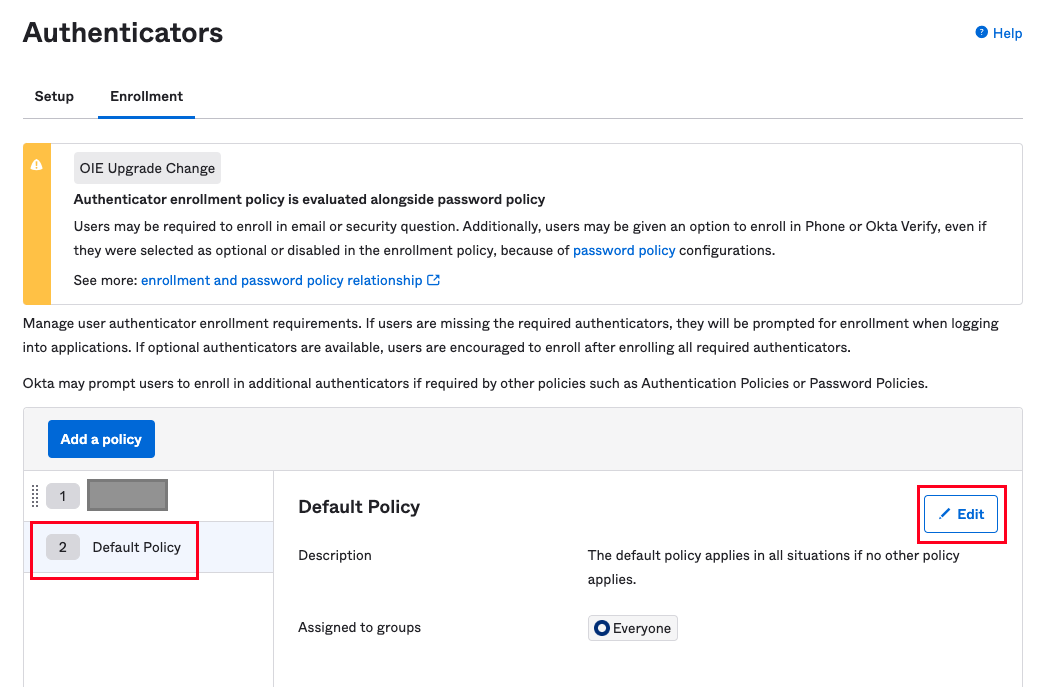
Modify Enrollment.
- Find the user authenticator, and select the behavior from the dropdown.
- Click Edit Policy to save changes.
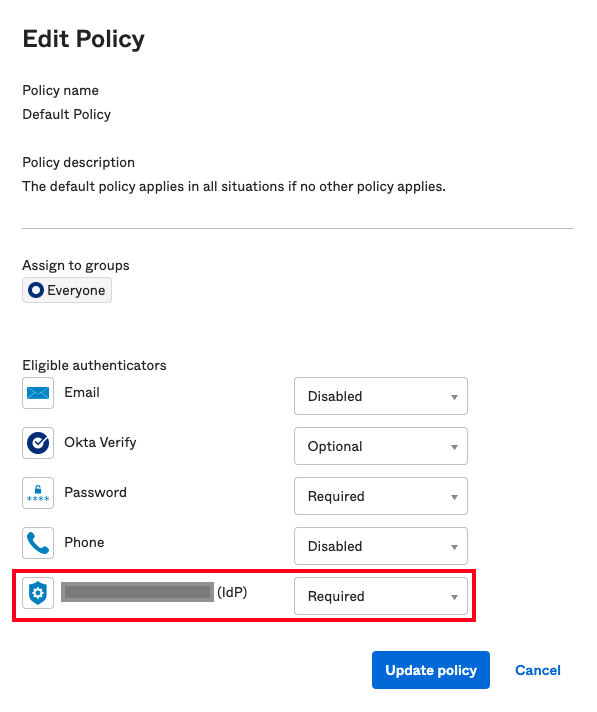
Modify Policy.
- User must add at least one rule to allow group members to enroll their authenticators.
- Click Add Rule below Eligible authenticators
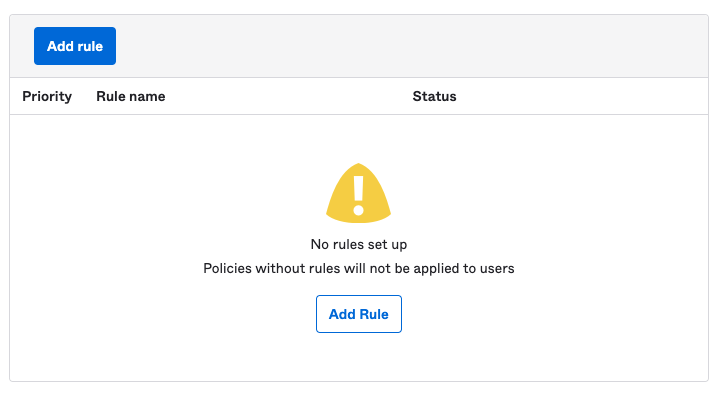
Add Rule.
- Accept the default settings and click Create Rule . It allows anyone in the applicable group to enroll their authenticators. Users can later add rules to exclude users based on name, IP address, or other attributes.
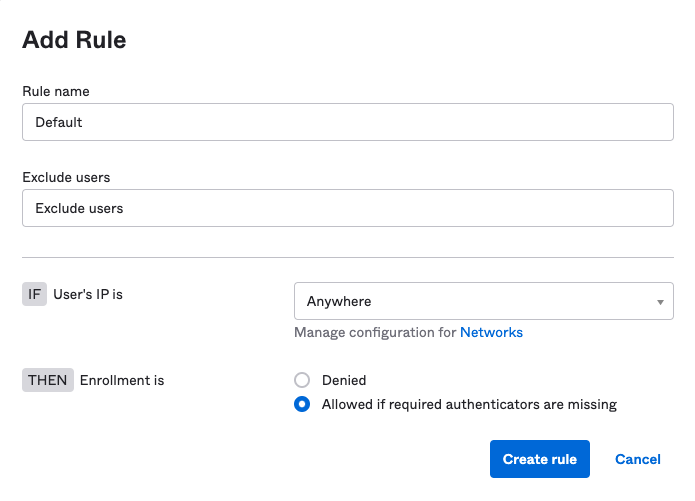
Create Rule.
Create Authentication Policy
Authentication policies are used to control when and where user-configured authenticators are applied.
To edit or add policies,
- Navigate to Security > Authentication Policies.
- Click an existing policy to edit it, or click Add a policy to create a new one.
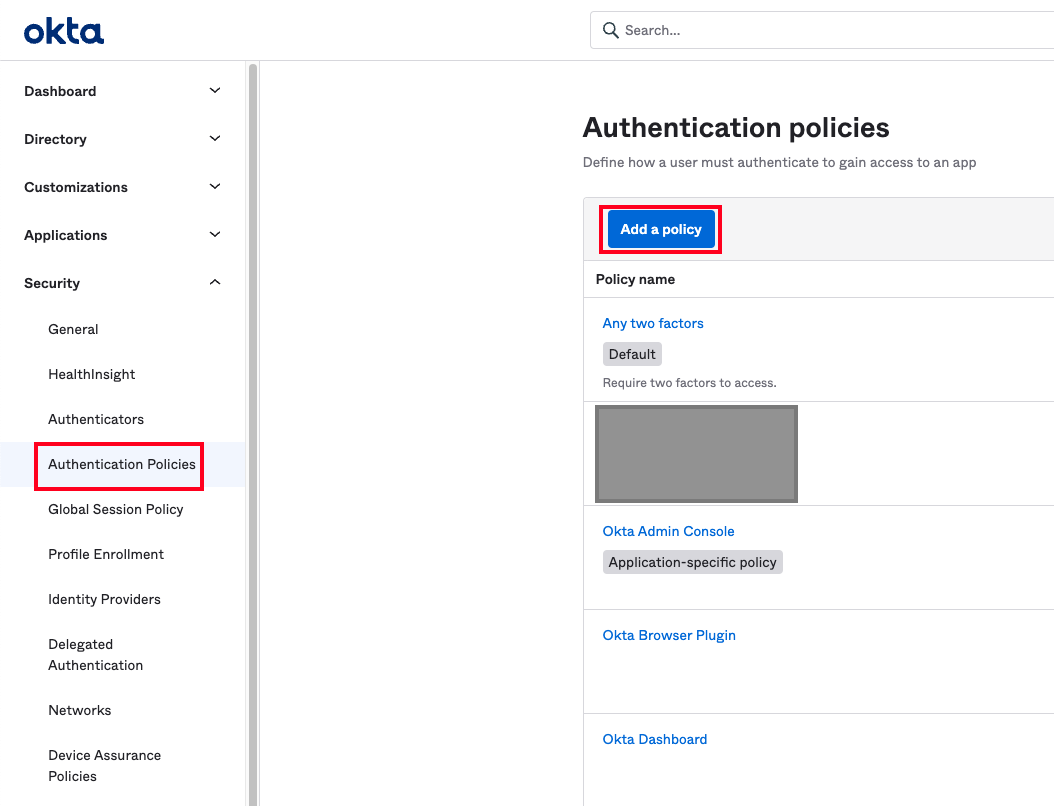
Authentication Policies.
- After creating a policy, click on the existing one, and the user is re-directed to the Rules tab. By default, every policy catch-all Rule if no other rules apply. Again, the user can either edit this rule or add a new one, click Add Rule:
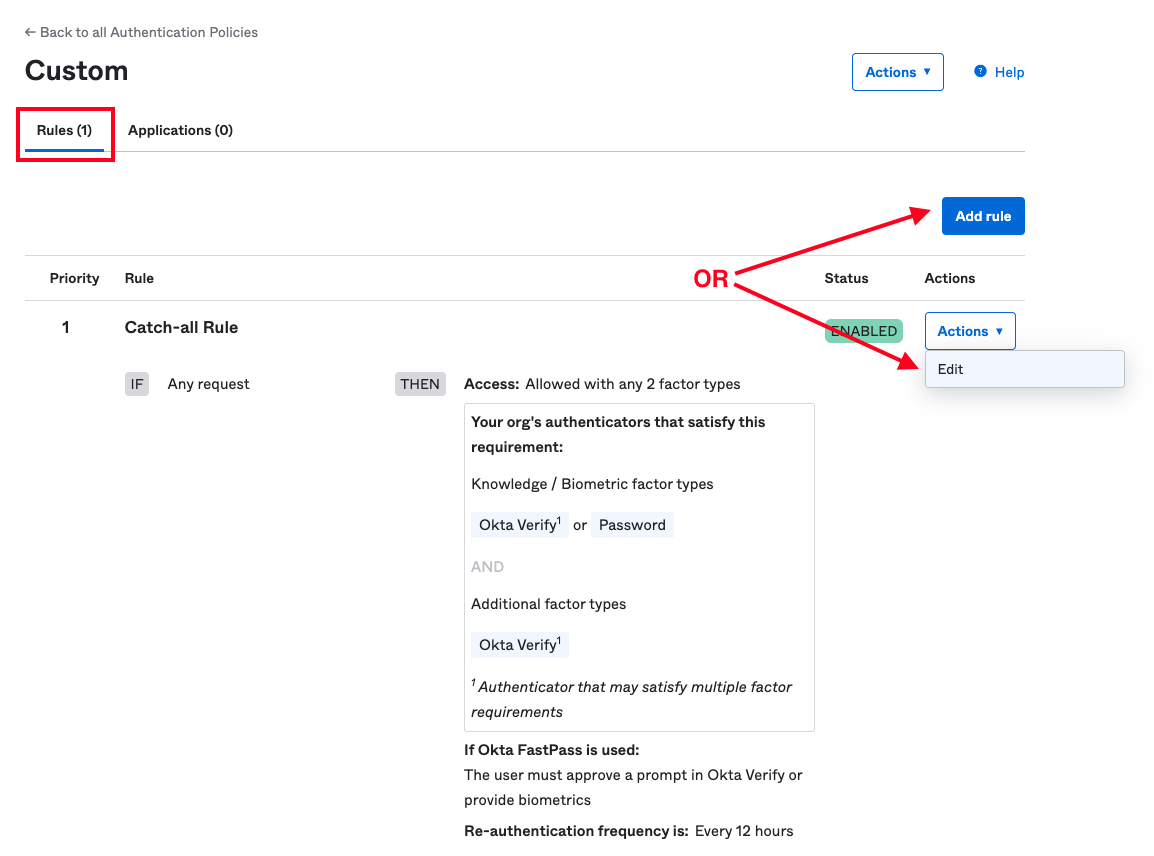
Rules
- First, specify a name and the conditions in which the rule gets activated.
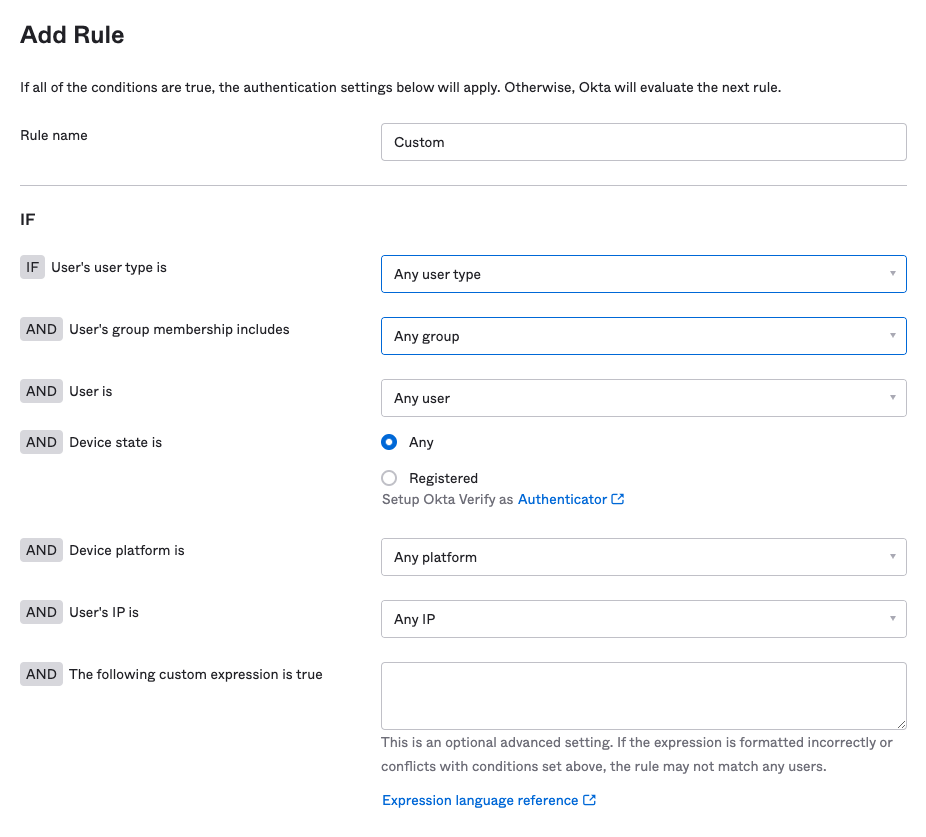
Add Rule
- For the outcome of a match, set the authenticate behavior to use anything except Password / IdP. Uncheck the box marked Exclude phone and email authenticators under the Possession factor constraints section. The user must see the IdP authenticator user configured earlier in the box below:
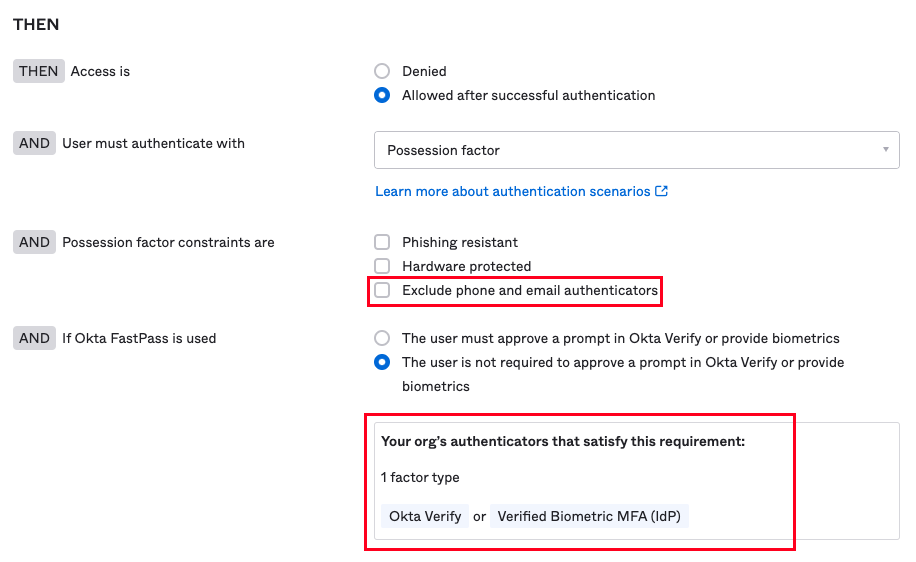
- Set the frequency for re-authentication to the appropriate value and click Save.
- Next, specify the applications rule applies to by navigating to the Applications tab of the policy details, and click Add app:
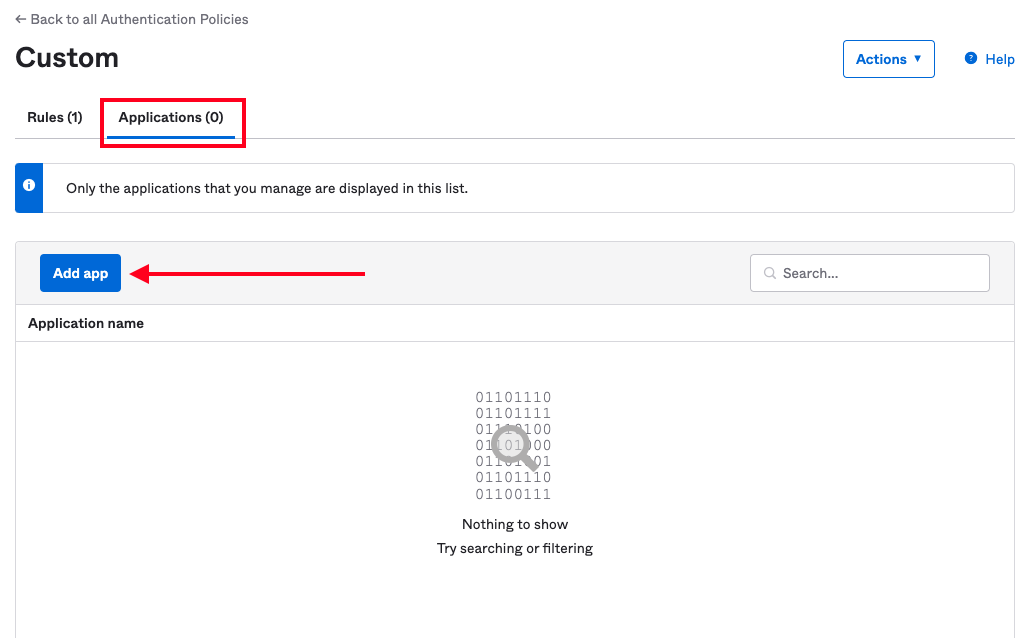
Custom Application.
- Select the applications for which the user is required to apply the authentication policy, and then close the dialog. User must see the apps listed on the page:
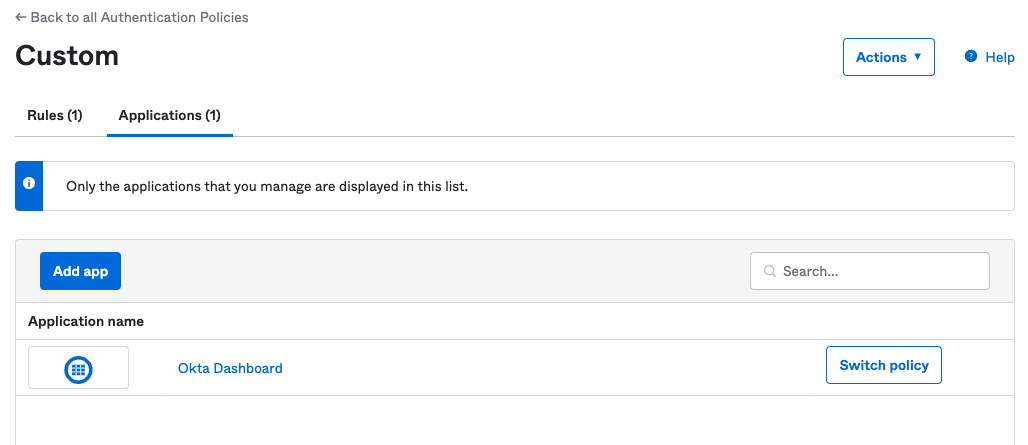
Add Custom Application.
Updated 7 months ago