VMware Workspace ONE Walkthrough
VMware Workspace ONE Walkthrough
The following steps demonstrate, how to set up an OIDC connection within the Workspace ONE Access Console that leverages AuthID's biometric authentication platform. The steps to fully integrate authID are as follows:
- Create a new integration in the authID Identity Portal.
- Configure authID as an identity provider within the Workspace ONE Access Console.
- Create and test access policy configuration.
Add Identity Provider
First, navigate to the Integrations > Identity Providers section from the user's dashboard and click the labeled Add Identity Provider. Select the option marked Create OpenID Connect IDP.
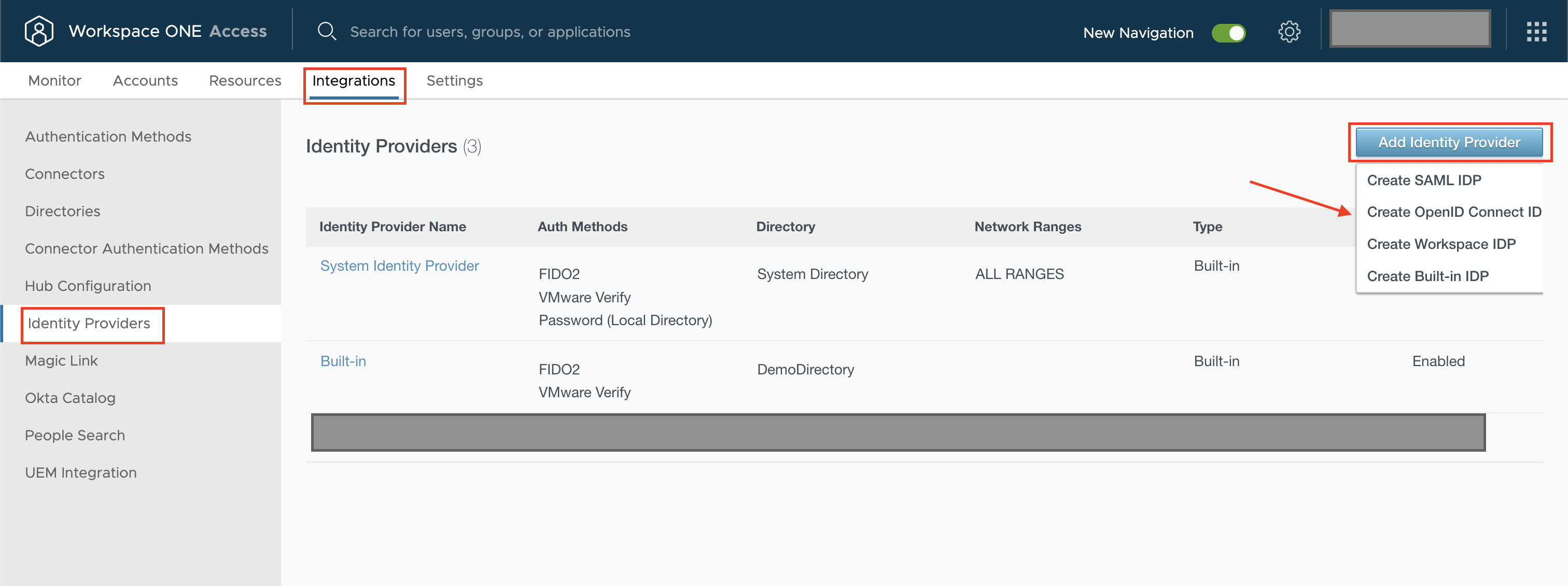
Identity Providers.
Select Automatic Discovery for the Authentication Configuration section and paste in the following value:
<https://id.authid.ai/oidc/web/.well-known/openid-configuration>Use the saved values from authID integration to fill out the Client ID and the Client Secret fields.
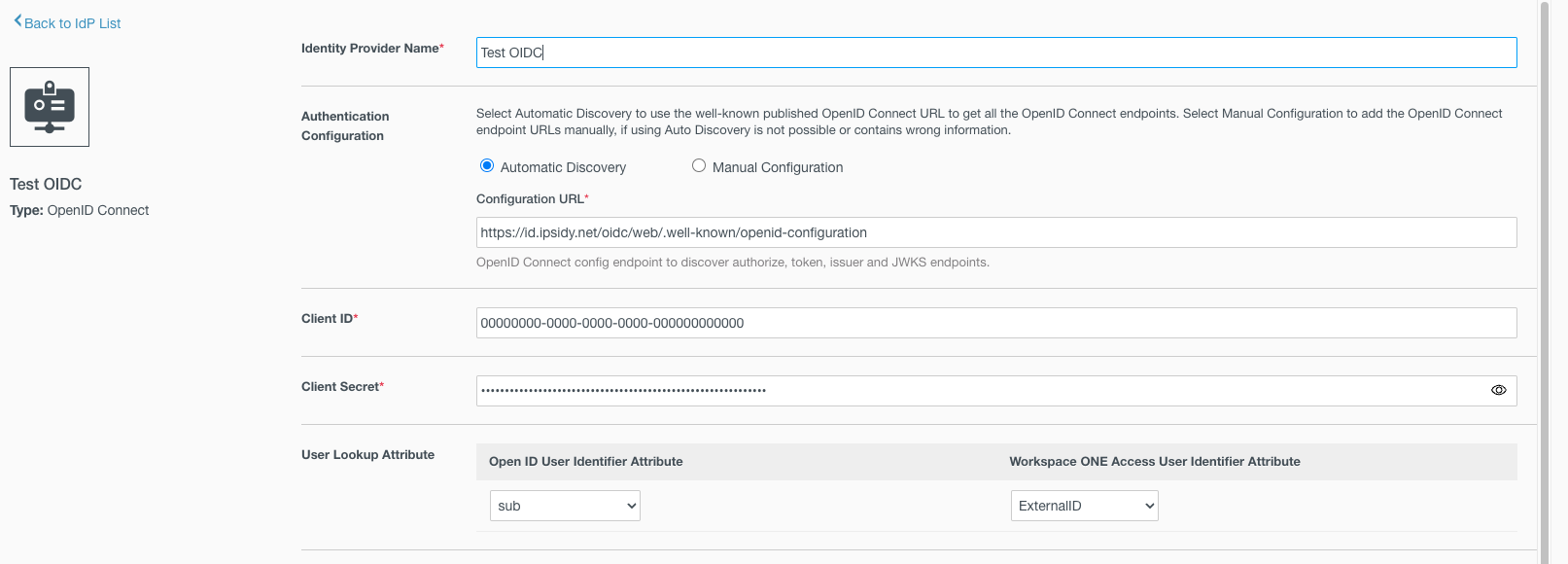
INFO: If users wish can enable Just-in-time user provisioning. Specify a directory name, domains, and user attribute mappings.
Finally, enable ALL RANGES and give a name that is used later as part of an Access Policy. Turn on Pass through Claims, and save to create the identity provider.
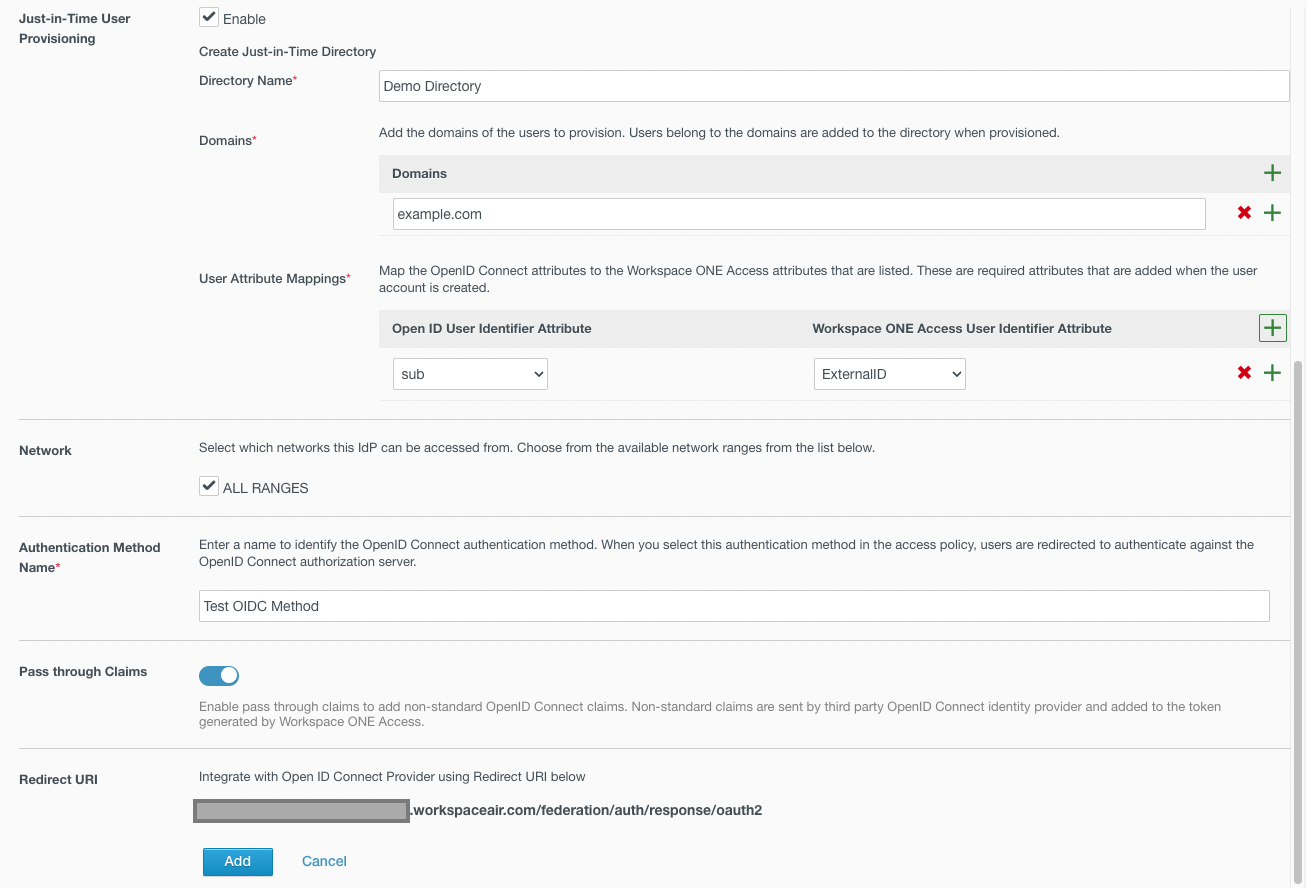
Add.
CAUTION
Once the identity provider has been created, user must ensure that at least one value from the Login redirect Urls parameter for user authID integration matches the Redirect URI. This value can be found at the bottom of the creation screen in the screenshot above.
Add Authentication Policy
Authentication policies are used to direct users to the preferred identity provider based on their conformance to the conditions set forth. In this way, the user can decide to send a subset of the user population through the OIDC identity provider we have created. To begin, navigate to the Resources > Policies section of the user dashboard and edit the default_access_policy_set or create a new one by clicking ADD POLICY.
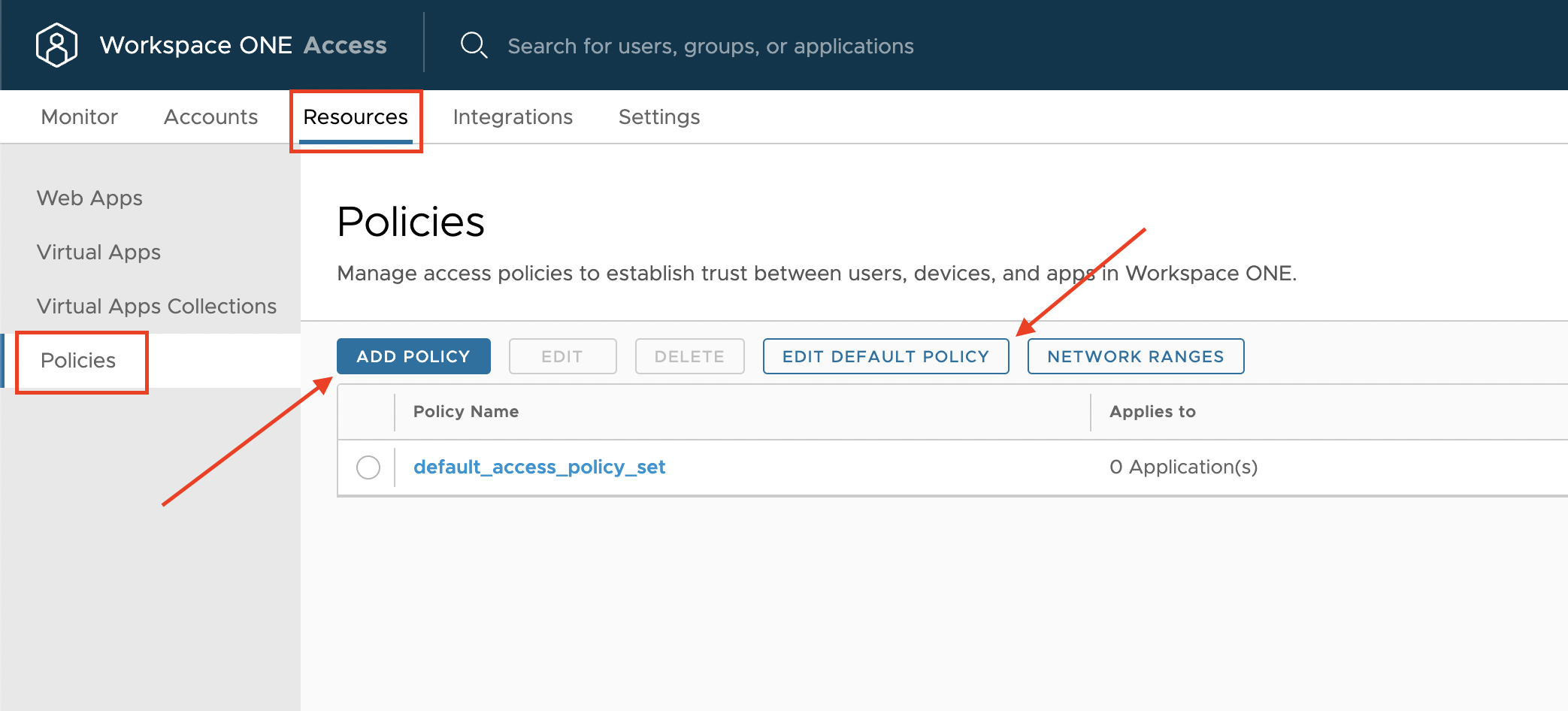
Policies.
Users can configure the rule as the user sees fit, but ensure that the section for authentication method points to the identity provider created earlier.
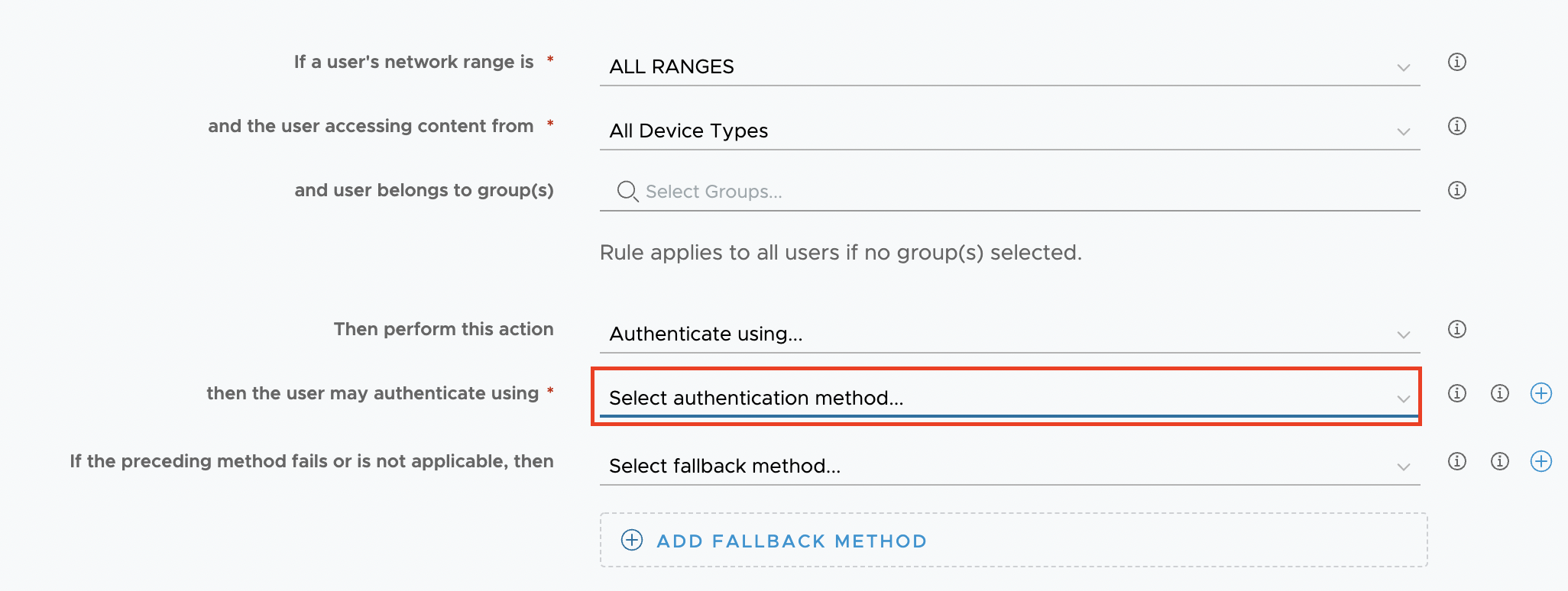
Authentication Method.
Testing the Policy
To test the effect of the policy, the user can log in as a member of the group to activate such a policy. The user must see the authID experience appear in the browser:
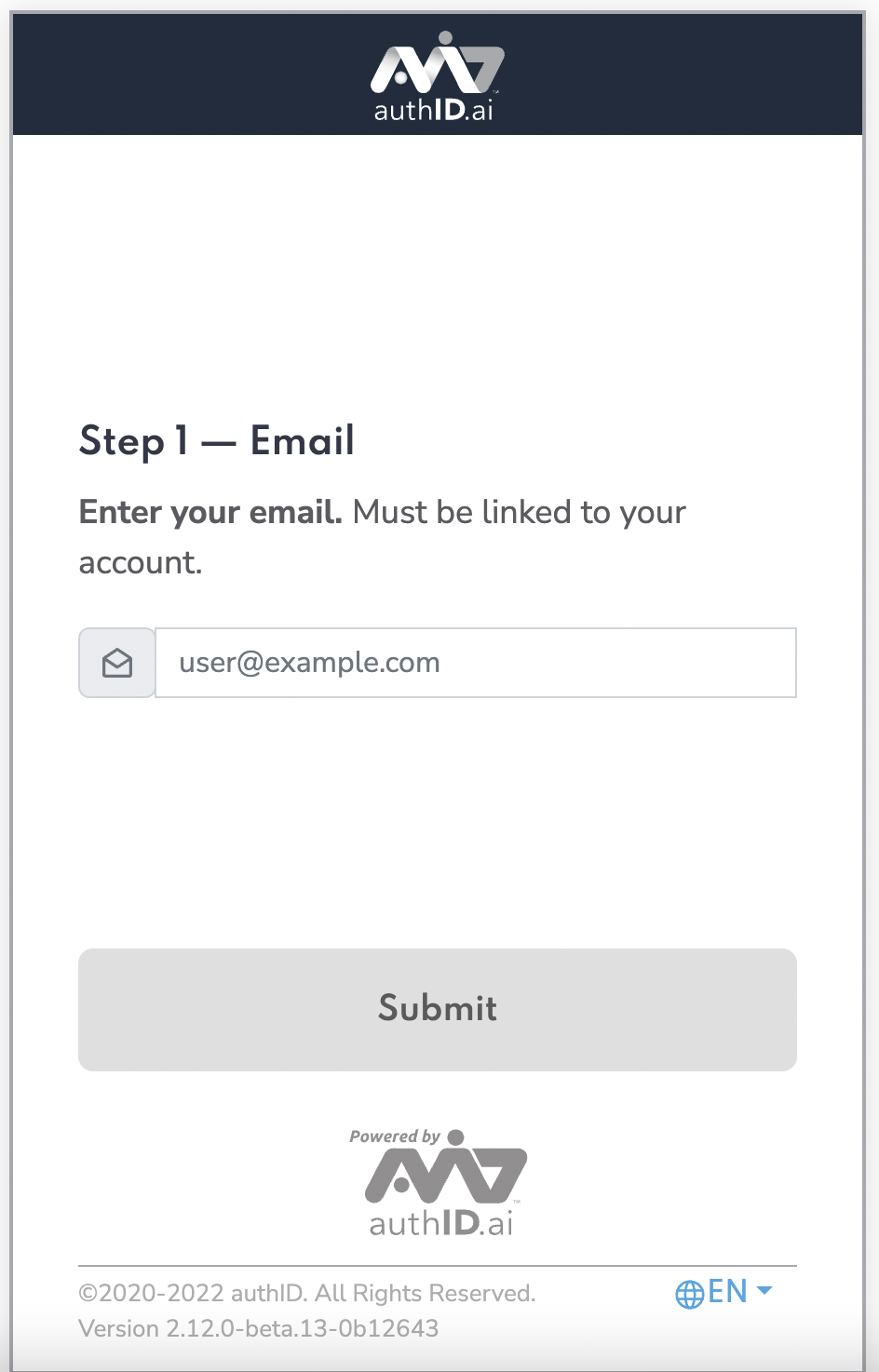
Enter Email.
Updated 7 months ago